Language: English. Brand New Book. While cryptography can still be a controversial topic in the programming community, Java has weathered that storm and provides a rich set of APIs that allow you, the developer, to effectively include cryptography in applications-if you know how. This book teaches you how. Chapters one through five cover the architecture of the JCE and JCA, symmetric and asymmetric key encryption in Java, message authentication codes, and how to create Java implementations with the API provided by the Bouncy Castle ASN.1 packages, all with plenty of examples. Building on that foundation, the second half of the book takes you into higher-level topics, enabling you to create and implement secure Java applications and make use of standard protocols such as CMS, SSL, and S/MIME.This book shows how to understand and use JCE, JCA, and the JSSE for encryption and authentication. It provides the ways in which padding mechanisms work in ciphers and how to spot and fix typical errors.
It offers an understanding of how authentication mechanisms are implemented in Java and why they are used. It provides methods for describing cryptographic objects with ASN.1. It shows how to create certificate revocation lists and use the Online Certificate Status Protocol (OCSP). It includes real-world Web solutions using Bouncy Castle APIs.This book is for Java developers who want to use cryptography in their applications or to understand how cryptography is being used in Java applications.
Knowledge of the Java language is necessary, but you need not be familiar with any of the APIs discussed. Wrox Beginning guides are crafted to make learning programming languages and technologies easier than you think, providing a structured, tutorial format that will guide you through all the techniques involved.
Bookseller Inventory # AAH339. Synopsis: Beginning Cryptography with Java While cryptography can still be a controversial topic in theprogramming community, Java has weathered that storm and provides arich set of APIs that allow you, the developer, to effectivelyinclude cryptography in applications-if you know how. This book teaches you how. Chapters one through five cover thearchitecture of the JCE and JCA, symmetric and asymmetric keyencryption in Java, message authentication codes, and how to createJava implementations with the API provided by the Bouncy CastleASN.1 packages, all with plenty of examples. Building on thatfoundation, the second half of the book takes you into higher-leveltopics, enabling you to create and implement secure Javaapplications and make use of standard protocols such as CMS, SSL,and S/MIME.
Book Depository is an international bookseller. We ship our books to over 100 countries around the globe and we are always looking to add more countries to the list. We really, really love books and offer millions of titles, currently over 10 million of them, with this figure increasing daily. Living by our motto, 'Bookseller to the World', we focus on offering as many titles as possible to as many customers as possible. Most of our titles are dispatched within 2 business days of your order.
Apart from publishers, distributors and wholesalers, we even list and supply books from other retailers! We hope you enjoy our selection and discover your new favorite book. Terms of Sale: All books are shipped in New condition promptly, we are happy to accept returns up to 30 days from purchase. Orders usually ship within 1-2 business days. Domestic Shipments are sent by Royal Mail, and International by Priority Airmail. We are happy to accept returns up to 30 days from purchase. Please contact the seller directly if you wish to return an order.
Name of business: The Book Depository Ltd Form of legal entity: A Limited Company Business address: The Book Depository, 60 Holborn Vi.
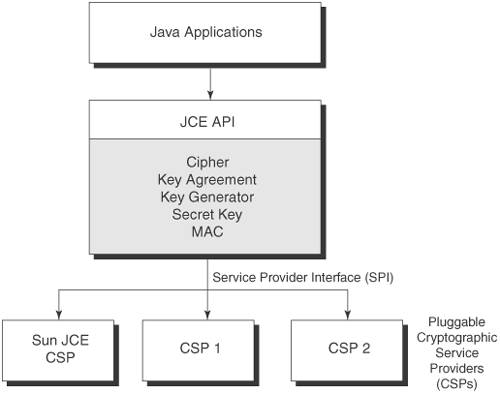
This class provides the functionality of a cryptographic cipher for encryption and decryption. It forms the core of the Java Cryptographic Extension (JCE) framework. In order to create a Cipher object, the application calls the Cipher's getInstance method, and passes the name of the requested transformation to it. Optionally, the name of a provider may be specified. A transformation is a string that describes the operation (or set of operations) to be performed on the given input, to produce some output.
A transformation always includes the name of a cryptographic algorithm (e.g., AES), and may be followed by a feedback mode and padding scheme. A transformation is of the form:. ' algorithm/mode/padding' or. ' algorithm' (in the latter case, provider-specific default values for the mode and padding scheme are used). For example, the following is a valid transformation: Cipher c = Cipher.getInstance(' AES/CBC/PKCS5Padding'); Using modes such as CFB and OFB, block ciphers can encrypt data in units smaller than the cipher's actual block size. When requesting such a mode, you may optionally specify the number of bits to be processed at a time by appending this number to the mode name as shown in the ' AES/CFB8/NoPadding' and ' AES/OFB32/PKCS5Padding' transformations.

If no such number is specified, a provider-specific default is used. Thus, block ciphers can be turned into byte-oriented stream ciphers by using an 8 bit mode such as CFB8 or OFB8. Modes such as Authenticated Encryption with Associated Data (AEAD) provide authenticity assurances for both confidential data and Additional Associated Data (AAD) that is not encrypted. (Please see for more information on AEAD and AEAD algorithms such as GCM/CCM.) Both confidential and AAD data can be used when calculating the authentication tag (similar to a ). This tag is appended to the ciphertext during encryption, and is verified on decryption. AEAD modes such as GCM/CCM perform all AAD authenticity calculations before starting the ciphertext authenticity calculations. To avoid implementations having to internally buffer ciphertext, all AAD data must be supplied to GCM/CCM implementations (via the updateAAD methods) before the ciphertext is processed (via the update and doFinal methods).
Note that GCM mode has a uniqueness requirement on IVs used in encryption with a given key. When IVs are repeated for GCM encryption, such usages are subject to forgery attacks. Thus, after each encryption operation using GCM mode, callers should re-initialize the cipher objects with GCM parameters which has a different IV value.
GCMParameterSpec s =.; cipher.init(., s); // If the GCM parameters were generated by the provider, it can // be retrieved by: // cipher.getParameters.getParameterSpec(GCMParameterSpec.class); cipher.updateAAD(.); // AAD cipher.update(.); // Multi-part update cipher.doFinal(.); // conclusion of operation // Use a different IV value for every encryption byte newIv =.; s = new GCMParameterSpec(s.getTLen, newIv); cipher.init(., s). Returns a Cipher object that implements the specified transformation. This method traverses the list of registered security Providers, starting with the most preferred Provider. A new Cipher object encapsulating the CipherSpi implementation from the first Provider that supports the specified algorithm is returned. Note that the list of registered providers may be retrieved via the method. Parameters: transformation - the name of the transformation, e.g., AES/CBC/PKCS5Padding. See the Cipher section in the for information about standard transformation names.
Returns: a cipher that implements the requested transformation. Throws: - if transformation is null, empty, in an invalid format, or if no Provider supports a CipherSpi implementation for the specified algorithm. if transformation contains a padding scheme that is not available. See Also:. getInstance public static final getInstance( transformation, provider) throws. Returns a Cipher object that implements the specified transformation.
A new Cipher object encapsulating the CipherSpi implementation from the specified provider is returned. The specified provider must be registered in the security provider list. Note that the list of registered providers may be retrieved via the method. Parameters: transformation - the name of the transformation, e.g., AES/CBC/PKCS5Padding.
See the Cipher section in the for information about standard transformation names. Provider - the name of the provider.
Returns: a cipher that implements the requested transformation. Throws: - if transformation is null, empty, in an invalid format, or if a CipherSpi implementation for the specified algorithm is not available from the specified provider. if the specified provider is not registered in the security provider list. if transformation contains a padding scheme that is not available. if the provider is null or empty.
See Also:. getInstance public static final getInstance( transformation, provider) throws. Returns a Cipher object that implements the specified transformation.
A new Cipher object encapsulating the CipherSpi implementation from the specified Provider object is returned. Note that the specified Provider object does not have to be registered in the provider list. Parameters: transformation - the name of the transformation, e.g., AES/CBC/PKCS5Padding.
See the Cipher section in the for information about standard transformation names. Provider - the provider.
Returns: a cipher that implements the requested transformation. Throws: - if transformation is null, empty, in an invalid format, or if a CipherSpi implementation for the specified algorithm is not available from the specified Provider object. if transformation contains a padding scheme that is not available. if the provider is null. See Also:. getProvider public final getProvider. Returns the length in bytes that an output buffer would need to be in order to hold the result of the next update or doFinal operation, given the input length inputLen (in bytes).
This call takes into account any unprocessed (buffered) data from a previous update call, padding, and AEAD tagging. The actual output length of the next update or doFinal call may be smaller than the length returned by this method. Parameters: inputLen - the input length (in bytes) Returns: the required output buffer size (in bytes) Throws: - if this cipher is in a wrong state (e.g., has not yet been initialized). getIV public final byte getIV. Initializes this cipher with a key. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters that cannot be derived from the given key, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidKeyException if it is being initialized for decryption or key unwrapping.
The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail.
If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them using the implementation of the highest-priority installed provider as the source of randomness. (If none of the installed providers supply an implementation of SecureRandom, a system-provided source of randomness will be used.) Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the key Throws: - if the given key is inappropriate for initializing this cipher, or requires algorithm parameters that cannot be determined from the given key, or if the given key has a keysize that exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files).
if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi. init public final void init(int opmode, key, random) throws. Initializes this cipher with a key and a source of randomness. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters that cannot be derived from the given key, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidKeyException if it is being initialized for decryption or key unwrapping.
The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them from random. Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the encryption key random - the source of randomness Throws: - if the given key is inappropriate for initializing this cipher, or requires algorithm parameters that cannot be determined from the given key, or if the given key has a keysize that exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi.
init public final void init(int opmode, key, params) throws. Initializes this cipher with a key and a set of algorithm parameters. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters and params is null, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidAlgorithmParameterException if it is being initialized for decryption or key unwrapping.
The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them using the implementation of the highest-priority installed provider as the source of randomness. (If none of the installed providers supply an implementation of SecureRandom, a system-provided source of randomness will be used.) Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it.
Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the encryption key params - the algorithm parameters Throws: - if the given key is inappropriate for initializing this cipher, or its keysize exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files). if the given algorithm parameters are inappropriate for this cipher, or this cipher requires algorithm parameters and params is null, or the given algorithm parameters imply a cryptographic strength that would exceed the legal limits (as determined from the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi.
init public final void init(int opmode, key, params, random) throws. Initializes this cipher with a key, a set of algorithm parameters, and a source of randomness. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters and params is null, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidAlgorithmParameterException if it is being initialized for decryption or key unwrapping. The generated parameters can be retrieved using or (if the parameter is an IV).
If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them from random. Note that when a Cipher object is initialized, it loses all previously-acquired state.
In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the encryption key params - the algorithm parameters random - the source of randomness Throws: - if the given key is inappropriate for initializing this cipher, or its keysize exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files). if the given algorithm parameters are inappropriate for this cipher, or this cipher requires algorithm parameters and params is null, or the given algorithm parameters imply a cryptographic strength that would exceed the legal limits (as determined from the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi. init public final void init(int opmode, key, params) throws.
Initializes this cipher with a key and a set of algorithm parameters. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters and params is null, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidAlgorithmParameterException if it is being initialized for decryption or key unwrapping. The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them using the implementation of the highest-priority installed provider as the source of randomness.
(If none of the installed providers supply an implementation of SecureRandom, a system-provided source of randomness will be used.) Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the encryption key params - the algorithm parameters Throws: - if the given key is inappropriate for initializing this cipher, or its keysize exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files). if the given algorithm parameters are inappropriate for this cipher, or this cipher requires algorithm parameters and params is null, or the given algorithm parameters imply a cryptographic strength that would exceed the legal limits (as determined from the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi. init public final void init(int opmode, key, params, random) throws. Initializes this cipher with a key, a set of algorithm parameters, and a source of randomness.
The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If this cipher requires any algorithm parameters and params is null, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidAlgorithmParameterException if it is being initialized for decryption or key unwrapping. The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail.
If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them from random. Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) key - the encryption key params - the algorithm parameters random - the source of randomness Throws: - if the given key is inappropriate for initializing this cipher, or its keysize exceeds the maximum allowable keysize (as determined from the configured jurisdiction policy files). if the given algorithm parameters are inappropriate for this cipher, or this cipher requires algorithm parameters and params is null, or the given algorithm parameters imply a cryptographic strength that would exceed the legal limits (as determined from the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi. init public final void init(int opmode, certificate) throws.
Initializes this cipher with the public key from the given certificate. The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If the certificate is of type X.509 and has a key usage extension field marked as critical, and the value of the key usage extension field implies that the public key in the certificate and its corresponding private key are not supposed to be used for the operation represented by the value of opmode, an InvalidKeyException is thrown. If this cipher requires any algorithm parameters that cannot be derived from the public key in the given certificate, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidKeyException if it is being initialized for decryption or key unwrapping.
The generated parameters can be retrieved using or (if the parameter is an IV). If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them using the SecureRandom implementation of the highest-priority installed provider as the source of randomness.
(If none of the installed providers supply an implementation of SecureRandom, a system-provided source of randomness will be used.) Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it. Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) certificate - the certificate Throws: - if the public key in the given certificate is inappropriate for initializing this cipher, or this cipher requires algorithm parameters that cannot be determined from the public key in the given certificate, or the keysize of the public key in the given certificate has a keysize that exceeds the maximum allowable keysize (as determined by the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi. init public final void init(int opmode, certificate, random) throws. Initializes this cipher with the public key from the given certificate and a source of randomness.
The cipher is initialized for one of the following four operations: encryption, decryption, key wrapping or key unwrapping, depending on the value of opmode. If the certificate is of type X.509 and has a key usage extension field marked as critical, and the value of the key usage extension field implies that the public key in the certificate and its corresponding private key are not supposed to be used for the operation represented by the value of opmode, an InvalidKeyException is thrown. If this cipher requires any algorithm parameters that cannot be derived from the public key in the given certificate, the underlying cipher implementation is supposed to generate the required parameters itself (using provider-specific default or random values) if it is being initialized for encryption or key wrapping, and raise an InvalidKeyException if it is being initialized for decryption or key unwrapping. The generated parameters can be retrieved using or (if the parameter is an IV).
If this cipher requires algorithm parameters that cannot be derived from the input parameters, and there are no reasonable provider-specific default values, initialization will necessarily fail. If this cipher (including its underlying feedback or padding scheme) requires any random bytes (e.g., for parameter generation), it will get them from random.
Note that when a Cipher object is initialized, it loses all previously-acquired state. In other words, initializing a Cipher is equivalent to creating a new instance of that Cipher and initializing it.
Parameters: opmode - the operation mode of this cipher (this is one of the following: ENCRYPTMODE, DECRYPTMODE, WRAPMODE or UNWRAPMODE) certificate - the certificate random - the source of randomness Throws: - if the public key in the given certificate is inappropriate for initializing this cipher, or this cipher requires algorithm parameters that cannot be determined from the public key in the given certificate, or the keysize of the public key in the given certificate has a keysize that exceeds the maximum allowable keysize (as determined by the configured jurisdiction policy files). if (@code opmode is WRAPMODE or UNWRAPMODE but the mode is not implemented by the underlying CipherSpi.
update public final byte update(byte input). Continues a multiple-part encryption or decryption operation (depending on how this cipher was initialized), processing another data part. The bytes in the input buffer are processed, and the result is stored in a new buffer. If input has a length of zero, this method returns null.
Parameters: input - the input buffer Returns: the new buffer with the result, or null if the underlying cipher is a block cipher and the input data is too short to result in a new block. Throws: - if this cipher is in a wrong state (e.g., has not been initialized). update public final byte update(byte input, int inputOffset, int inputLen).
Continues a multiple-part encryption or decryption operation (depending on how this cipher was initialized), processing another data part. The first inputLen bytes in the input buffer, starting at inputOffset inclusive, are processed, and the result is stored in a new buffer. If inputLen is zero, this method returns null. Parameters: input - the input buffer inputOffset - the offset in input where the input starts inputLen - the input length Returns: the new buffer with the result, or null if the underlying cipher is a block cipher and the input data is too short to result in a new block.
Throws: - if this cipher is in a wrong state (e.g., has not been initialized). update public final int update(byte input, int inputOffset, int inputLen, byte output) throws. Continues a multiple-part encryption or decryption operation (depending on how this cipher was initialized), processing another data part. The first inputLen bytes in the input buffer, starting at inputOffset inclusive, are processed, and the result is stored in the output buffer. If the output buffer is too small to hold the result, a ShortBufferException is thrown.
In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be. If inputLen is zero, this method returns a length of zero. Note: this method should be copy-safe, which means the input and output buffers can reference the same byte array and no unprocessed input data is overwritten when the result is copied into the output buffer. Parameters: input - the input buffer inputOffset - the offset in input where the input starts inputLen - the input length output - the buffer for the result Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if the given output buffer is too small to hold the result. update public final int update(byte input, int inputOffset, int inputLen, byte output, int outputOffset) throws. Continues a multiple-part encryption or decryption operation (depending on how this cipher was initialized), processing another data part.
The first inputLen bytes in the input buffer, starting at inputOffset inclusive, are processed, and the result is stored in the output buffer, starting at outputOffset inclusive. If the output buffer is too small to hold the result, a ShortBufferException is thrown. In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be. If inputLen is zero, this method returns a length of zero. Note: this method should be copy-safe, which means the input and output buffers can reference the same byte array and no unprocessed input data is overwritten when the result is copied into the output buffer. Parameters: input - the input buffer inputOffset - the offset in input where the input starts inputLen - the input length output - the buffer for the result outputOffset - the offset in output where the result is stored Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if the given output buffer is too small to hold the result.
update public final int update( input, output) throws. Continues a multiple-part encryption or decryption operation (depending on how this cipher was initialized), processing another data part. All input.remaining bytes starting at input.position are processed.
The result is stored in the output buffer. Upon return, the input buffer's position will be equal to its limit; its limit will not have changed. The output buffer's position will have advanced by n, where n is the value returned by this method; the output buffer's limit will not have changed. If output.remaining bytes are insufficient to hold the result, a ShortBufferException is thrown. In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be.
Note: this method should be copy-safe, which means the input and output buffers can reference the same block of memory and no unprocessed input data is overwritten when the result is copied into the output buffer. Parameters: input - the input ByteBuffer output - the output ByteByffer Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if input and output are the same object - if the output buffer is read-only - if there is insufficient space in the output buffer Since: 1.5. doFinal public final byte doFinal throws.
Finishes a multiple-part encryption or decryption operation, depending on how this cipher was initialized. Input data that may have been buffered during a previous update operation is processed, with padding (if requested) being applied. If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in a new buffer. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data.
Note: if any exception is thrown, this cipher object may need to be reset before it can be used again. Returns: the new buffer with the result Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided. if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value.
doFinal public final int doFinal(byte output, int outputOffset) throws. Finishes a multiple-part encryption or decryption operation, depending on how this cipher was initialized. Input data that may have been buffered during a previous update operation is processed, with padding (if requested) being applied. If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in the output buffer, starting at outputOffset inclusive. If the output buffer is too small to hold the result, a ShortBufferException is thrown.
In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data. Note: if any exception is thrown, this cipher object may need to be reset before it can be used again. Parameters: output - the buffer for the result outputOffset - the offset in output where the result is stored Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided. if the given output buffer is too small to hold the result - if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value.
doFinal public final byte doFinal(byte input) throws. Encrypts or decrypts data in a single-part operation, or finishes a multiple-part operation. The data is encrypted or decrypted, depending on how this cipher was initialized.
The bytes in the input buffer, and any input bytes that may have been buffered during a previous update operation, are processed, with padding (if requested) being applied. If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in a new buffer. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data.
Note: if any exception is thrown, this cipher object may need to be reset before it can be used again. Parameters: input - the input buffer Returns: the new buffer with the result Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided. if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value. doFinal public final byte doFinal(byte input, int inputOffset, int inputLen) throws. Encrypts or decrypts data in a single-part operation, or finishes a multiple-part operation. The data is encrypted or decrypted, depending on how this cipher was initialized. The first inputLen bytes in the input buffer, starting at inputOffset inclusive, and any input bytes that may have been buffered during a previous update operation, are processed, with padding (if requested) being applied.
If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in a new buffer. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data. Note: if any exception is thrown, this cipher object may need to be reset before it can be used again. Parameters: input - the input buffer inputOffset - the offset in input where the input starts inputLen - the input length Returns: the new buffer with the result Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided.
if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value. doFinal public final int doFinal(byte input, int inputOffset, int inputLen, byte output) throws. Encrypts or decrypts data in a single-part operation, or finishes a multiple-part operation. The data is encrypted or decrypted, depending on how this cipher was initialized. The first inputLen bytes in the input buffer, starting at inputOffset inclusive, and any input bytes that may have been buffered during a previous update operation, are processed, with padding (if requested) being applied.
If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in the output buffer. If the output buffer is too small to hold the result, a ShortBufferException is thrown. In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be.
Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data.
Note: if any exception is thrown, this cipher object may need to be reset before it can be used again. Note: this method should be copy-safe, which means the input and output buffers can reference the same byte array and no unprocessed input data is overwritten when the result is copied into the output buffer.
Parameters: input - the input buffer inputOffset - the offset in input where the input starts inputLen - the input length output - the buffer for the result Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided. if the given output buffer is too small to hold the result - if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value. doFinal public final int doFinal(byte input, int inputOffset, int inputLen, byte output, int outputOffset) throws. Encrypts or decrypts data in a single-part operation, or finishes a multiple-part operation. The data is encrypted or decrypted, depending on how this cipher was initialized.
The first inputLen bytes in the input buffer, starting at inputOffset inclusive, and any input bytes that may have been buffered during a previous update operation, are processed, with padding (if requested) being applied. If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in the output buffer, starting at outputOffset inclusive. If the output buffer is too small to hold the result, a ShortBufferException is thrown.
In this case, repeat this call with a larger output buffer. Use to determine how big the output buffer should be. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data. Note: if any exception is thrown, this cipher object may need to be reset before it can be used again.
Note: this method should be copy-safe, which means the input and output buffers can reference the same byte array and no unprocessed input data is overwritten when the result is copied into the output buffer. Encrypts or decrypts data in a single-part operation, or finishes a multiple-part operation. The data is encrypted or decrypted, depending on how this cipher was initialized. All input.remaining bytes starting at input.position are processed. If an AEAD mode such as GCM/CCM is being used, the authentication tag is appended in the case of encryption, or verified in the case of decryption. The result is stored in the output buffer. Upon return, the input buffer's position will be equal to its limit; its limit will not have changed.
The output buffer's position will have advanced by n, where n is the value returned by this method; the output buffer's limit will not have changed. If output.remaining bytes are insufficient to hold the result, a ShortBufferException is thrown. In this case, repeat this call with a larger output buffer.
Use to determine how big the output buffer should be. Upon finishing, this method resets this cipher object to the state it was in when previously initialized via a call to init. That is, the object is reset and available to encrypt or decrypt (depending on the operation mode that was specified in the call to init) more data. Note: if any exception is thrown, this cipher object may need to be reset before it can be used again.
Note: this method should be copy-safe, which means the input and output buffers can reference the same byte array and no unprocessed input data is overwritten when the result is copied into the output buffer. Parameters: input - the input ByteBuffer output - the output ByteBuffer Returns: the number of bytes stored in output Throws: - if this cipher is in a wrong state (e.g., has not been initialized) - if input and output are the same object - if the output buffer is read-only - if this cipher is a block cipher, no padding has been requested (only in encryption mode), and the total input length of the data processed by this cipher is not a multiple of block size; or if this encryption algorithm is unable to process the input data provided. if there is insufficient space in the output buffer - if this cipher is in decryption mode, and (un)padding has been requested, but the decrypted data is not bounded by the appropriate padding bytes - if this cipher is decrypting in an AEAD mode (such as GCM/CCM), and the received authentication tag does not match the calculated value Since: 1.5. wrap public final byte wrap( key) throws. Parameters: key - the key to be wrapped.
Returns: the wrapped key. Throws: - if this cipher is in a wrong state (e.g., has not been initialized). if this cipher is a block cipher, no padding has been requested, and the length of the encoding of the key to be wrapped is not a multiple of the block size.
if it is impossible or unsafe to wrap the key with this cipher (e.g., a hardware protected key is being passed to a software-only cipher). if the corresponding method in the CipherSpi is not supported. unwrap public final unwrap(byte wrappedKey, wrappedKeyAlgorithm, int wrappedKeyType) throws. Unwrap a previously wrapped key.
Parameters: wrappedKey - the key to be unwrapped. WrappedKeyAlgorithm - the algorithm associated with the wrapped key. WrappedKeyType - the type of the wrapped key. This must be one of SECRETKEY, PRIVATEKEY, or PUBLICKEY. Returns: the unwrapped key. Throws: - if this cipher is in a wrong state (e.g., has not been initialized).
if no installed providers can create keys of type wrappedKeyType for the wrappedKeyAlgorithm. if wrappedKey does not represent a wrapped key of type wrappedKeyType for the wrappedKeyAlgorithm.
if the corresponding method in the CipherSpi is not supported. getMaxAllowedKeyLength public static final int getMaxAllowedKeyLength( transformation) throws. Returns the maximum key length for the specified transformation according to the installed JCE jurisdiction policy files. If JCE unlimited strength jurisdiction policy files are installed, Integer.MAXVALUE will be returned. For more information on default key size in JCE jurisdiction policy files, please see Appendix E in the. Parameters: transformation - the cipher transformation.
Returns: the maximum key length in bits or Integer.MAXVALUE. Throws: - if transformation is null. if transformation is not a valid transformation, i.e. In the form of 'algorithm' or 'algorithm/mode/padding'. Since: 1.5. getMaxAllowedParameterSpec public static final getMaxAllowedParameterSpec( transformation) throws. Returns an AlgorithmParameterSpec object which contains the maximum cipher parameter value according to the jurisdiction policy file.
If JCE unlimited strength jurisdiction policy files are installed or there is no maximum limit on the parameters for the specified transformation in the policy file, null will be returned. Parameters: transformation - the cipher transformation. Returns: an AlgorithmParameterSpec which holds the maximum value or null. Throws: - if transformation is null. if transformation is not a valid transformation, i.e. In the form of 'algorithm' or 'algorithm/mode/padding'.
Since: 1.5. updateAAD public final void updateAAD(byte src).
Continues a multi-part update of the Additional Authentication Data (AAD). Calls to this method provide AAD to the cipher when operating in modes such as AEAD (GCM/CCM).
Beginning Cryptography With Java
If this cipher is operating in either GCM or CCM mode, all AAD must be supplied before beginning operations on the ciphertext (via the update and doFinal methods). Parameters: src - the buffer containing the Additional Authentication Data Throws: - if the src byte array is null - if this cipher is in a wrong state (e.g., has not been initialized), does not accept AAD, or if operating in either GCM or CCM mode and one of the update methods has already been called for the active encryption/decryption operation - if the corresponding method in the CipherSpi has not been overridden by an implementation Since: 1.7. updateAAD public final void updateAAD(byte src, int offset, int len).
Continues a multi-part update of the Additional Authentication Data (AAD), using a subset of the provided buffer. Calls to this method provide AAD to the cipher when operating in modes such as AEAD (GCM/CCM). If this cipher is operating in either GCM or CCM mode, all AAD must be supplied before beginning operations on the ciphertext (via the update and doFinal methods). Continues a multi-part update of the Additional Authentication Data (AAD). Calls to this method provide AAD to the cipher when operating in modes such as AEAD (GCM/CCM).

Beginning Cryptography With Java David Hook Pdf
If this cipher is operating in either GCM or CCM mode, all AAD must be supplied before beginning operations on the ciphertext (via the update and doFinal methods). All src.remaining bytes starting at src.position are processed. Upon return, the input buffer's position will be equal to its limit; its limit will not have changed. Parameters: src - the buffer containing the AAD Throws: - if the src ByteBuffer is null - if this cipher is in a wrong state (e.g., has not been initialized), does not accept AAD, or if operating in either GCM or CCM mode and one of the update methods has already been called for the active encryption/decryption operation - if the corresponding method in the CipherSpi has not been overridden by an implementation Since: 1.7.